When Windows Defender Met Server 2003: The Case of the Disappearing Security UI
A few weeks after successfully joining Windows 11 machines to a Windows Server 2003 domain, something odd happened: the Windows Security app on one of the clients went completely blank. No buttons, no icons – just a message claiming my machine wasn’t compatible. Local admins could see everything fine, but normal users were stuck staring at an empty UI.
I knew this had to be a Group Policy issue, but tracking it down turned into a classic case of legacy infrastructure meeting modern software.
Disclaimer: This is only when you are in a domain on a ancient 2003 server and set up BlockExe Files Policy!
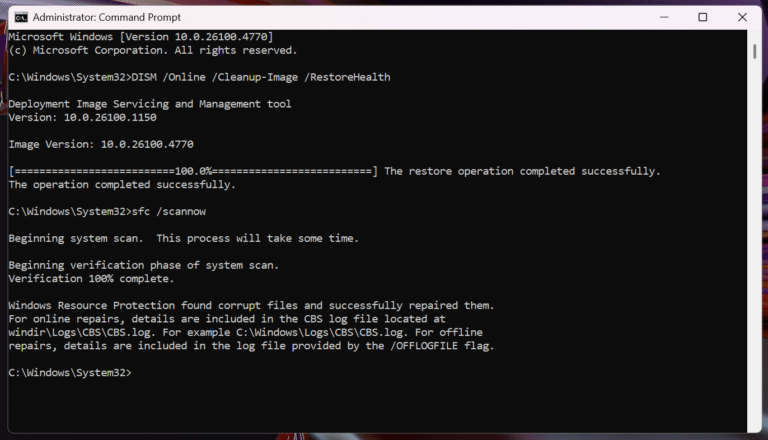
Diagnosing the Problem
The symptoms were clear: the client was fully functional in other respects – domain join succeeded, drives mapped correctly, and services were running. Only Windows Security refused to display for standard users.
The first suspect? A Software Restriction Policy (SRP) in the Server 2003 domain. The SRP was set to:
Default Security Level = Disallowed
Applied to all users except local and domain admins
A custom GPO named “Block exe files” existed
Interestingly, folders like C:\Program Files were marked as unrestricted. But Defender still wouldn’t open. Changing the SRP default to Unrestricted immediately fixed the issue – proving that SRP was indeed the culprit.
The Hidden Catch: Versioned Paths
Server 2003 SRP only works with literal paths – no wildcards or subfolder patterns. Meanwhile, Windows 11 Defender executables live in versioned subfolders that change with every platform update. For example:
C:\Windows\System32\SecurityHealth\10.0.27840.1000-0\SecurityHealthHost.exe
Every new Defender update generates a new folder name. Because SRP can’t handle wildcards, each new version appears as an unapproved path and gets blocked silently.
The Forensics: Tools and Clues
ProcMon didn’t show any file blocks at first – SRP blocks occurred too early for it to catch. Event Viewer came to the rescue. By enabling Audit Process Tracking and checking Event ID 4688, I found the exact executable path being blocked:
C:\Windows\System32\SecurityHealth\10.0.27840.1000-0\SecurityHealthHost.exe
This was the smoking gun.
The Fix
The solution was simple – once identified: whitelist the exact path for that Defender version.
Whitelisting C:\Windows\System32\SecurityHealth\10.0.27840.1000-0\SecurityHealthHost.exe restored the UI immediately.
Using wildcards like C:\Windows\System32\SecurityHealth\* failed because Server 2003 SRP doesn’t support them.
Because the folder changes with each update, this rule will need to be updated roughly once a month. Or we just have to update our ancient 2003 server.
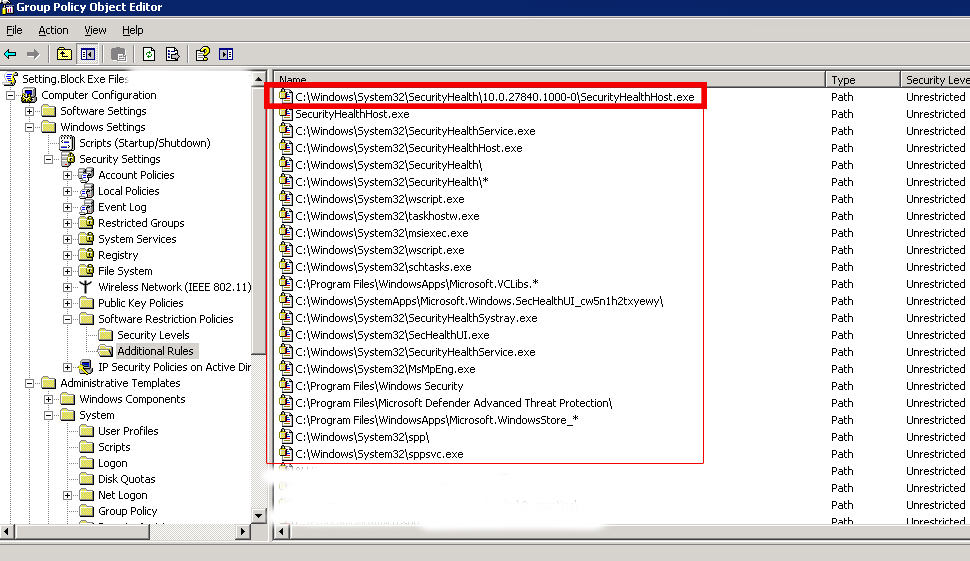
You can try other paths I did put in here. They can help you in your case!
C:\Windows\System32\SecHealthUI.exe
C:\Windows\System32\SecurityHealthService.exe
C:\Windows\System32\SecurityHealthSystray.exe
C:\Windows\System32\SecurityHealthHost.exe
C:\Windows\System32\SecurityHealth\
Lessons Learned
This issue wasn’t caused by Windows 11 or Defender, but by an SRP engine from 2003 trying to manage modern, dynamically updated executables. Server 2003 SRP can’t handle wildcard paths, and Windows 11 loves versioned directories – the perfect storm for a disappearing UI.
Sometimes, compatibility isn’t about what works — it’s about what quietly breaks in the background. Legacy systems may function, but modern software will always find ways to expose their limitations.
Conclusion
• Identified SRP as the blocker preventing Windows Security from opening.
• Confirmed the blocked path via Event ID 4688 logs.
• Whitelisted the exact Defender executable path for the current platform version.
Permanent resolution requires either manually updating the SRP for each Defender update or migrating the domain GPO to a newer server (2008 R2+) that supports wildcard SRP rules.



One Comment